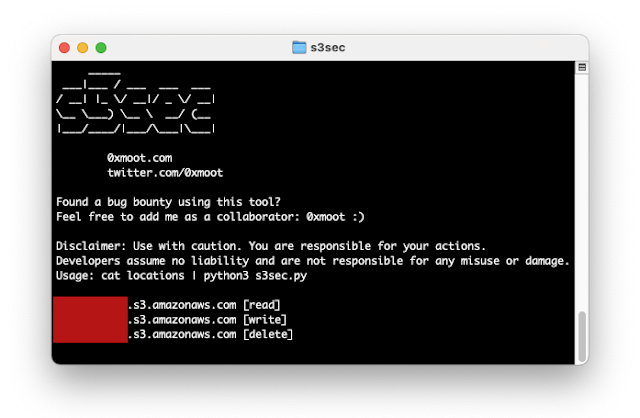
S3Sec - Check AWS S3 Instances For Read/Write/Delete Access
Test AWS S3 buckets for read/write/delete access
This tool was developed to quickly test a list of s3 buckets for public read, write and delete access for the purposes of penetration testing on bug bounty programs.
Found a bug bounty using this tool? Feel free to add me as a collaborator: @0xmoot :)
Installation
Clone the git repo onto your machine:
git clone https://github.com/0xmoot/s3secHappy hunting :)
Usage
Check a single S3 instance:
echo "test-instance.s3.amazonaws.com" | python3 s3sec.pyOr:
echo "test-instance" | python3 s3sec.pyCheck a list of S3 instances:
cat locations | python3 s3sec.pySetup AWS CLI & Credentials (optional)
To get the most out of this tool you should install the AWS CLI and setup user credentials.
With AWS CLI a series of deeper tests (including unsigned read, writing files and deleting files) is activated:
Installing AWS CLI on Kali Linux
To install AWS CLI you can simply install using below command:
pip3 install awscliGetting AWS Credentials (Access Key ID and AWS Secret Access Key)
-
Sign up for Amazon's AWS from their official website: https://aws.amazon.com/free/?all-free-tier.sort-by=item.additionalFields.SortRank&all-free-tier.sort-order=asc
-
Login into your AWS account and click on My Security Credentials.
-
Click on Access Keys (access key id and secret access key) to get your login credentials for AWS CLI.
-
Then click on Show Access Key option to get your Access Key ID and Secret Access Key or you can download it as well.
Configuring AWS CLI on Kali Linux
- Start a terminal and enter the below commands then enter the AWS Access Key ID and AWS Secret Access Key that was created in previous steps.
aws configureUse the following default settings:
AWS Access Key Id: <<Your Key>> AWS Secret Access Key: <<Your Secret Access Key>> Default region name: ap-south-1 Default output format: json Disclaimer
The developers assume no liability and are not responsible for any misuse or damage caused by the s3sec tool. The tool is provided as-is for educational and bug bounty purposes.
License
 Reviewed by Zion3R
on
8:30 AM
Rating:
Reviewed by Zion3R
on
8:30 AM
Rating: