autoSSRF - Smart Context-Based SSRF Vulnerabiltiy Scanner
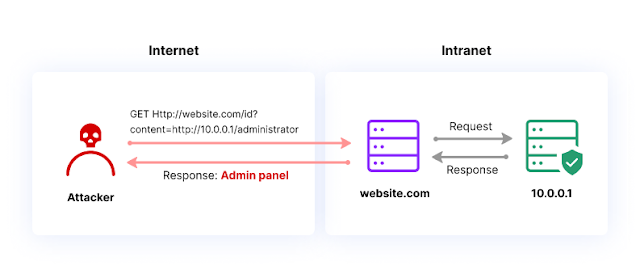
autoSSRF is your best ally for identifying SSRF vulnerabilities at scale. Different from other ssrf automation tools, this one comes with the two following original features :
-
Smart fuzzing on relevant SSRF GET parameters
When fuzzing, autoSSRF only focuses on the common parameters related to SSRF (
?url=,?uri=, ..) and doesn’t interfere with everything else. This ensures that the original URL is still correctly understood by the tested web-application, something that might doesn’t happen with a tool which is blindly spraying query parameters. -
Context-based dynamic payloads generation
For the given URL :
https://host.com/?fileURL=https://authorizedhost.com, autoSSRF would recognize authorizedhost.com as a potentially white-listed host for the web-application, and generate payloads dynamically based on that, attempting to bypass the white-listing validation. It would result to interesting payloads such as :http://authorizedhost.attacker.com,http://authorizedhost%[email protected], etc.
Furthermore, this tool guarantees almost no false-positives. The detection relies on the great ProjectDiscovery’s interactsh, allowing autoSSRF to confidently identify out-of-band DNS/HTTP interactions.
Usage
python3 autossrf.py -hThis displays help for the tool.
usage: autossrf.py [-h] [--file FILE] [--url URL] [--output] [--verbose]
options:
-h, --help show this help message and exit
--file FILE, -f FILE file of all URLs to be tested against SSRF
--url URL, -u URL url to be tested against SSRF
--output, -o output file path
--verbose, -v activate verbose modeSingle URL target:
python3 autossrf.py -u https://www.host.com/?param1=X¶m2=Y¶m2=ZMultiple URLs target with verbose:
python3 autossrf.py -f urls.txt -vInstallation
1 - Clone
git clone https://github.com/Th0h0/autossrf.git2 - Install requirements
Python libraries :
cd autossrf
pip install -r requirements.txtInteractsh-Client :
go install -v github.com/projectdiscovery/interactsh/cmd/interactsh-client@latestLicense
autoSSRF is distributed under MIT License.
 Reviewed by Zion3R
on
8:30 AM
Rating:
Reviewed by Zion3R
on
8:30 AM
Rating: