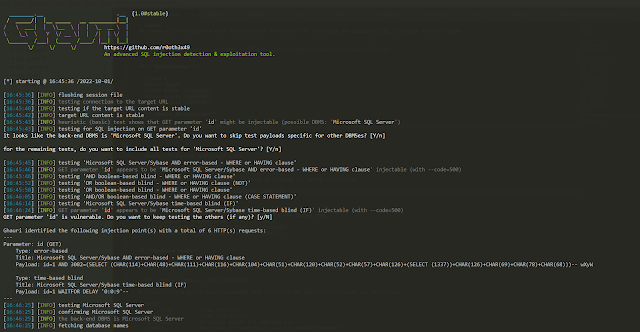
Ghauri - An Advanced Cross-Platform Tool That Automates The Process Of Detecting And Exploiting SQL Injection Security Flaws
An advanced cross-platform tool that automates the process of detecting and exploiting SQL injection security flaws
Requirements
- Python 3
- Python
pip3
Installation
- cd to ghauri directory.
- install requirements:
python3 -m pip install --upgrade -r requirements.txt - run:
python3 setup.py installorpython3 -m pip install -e . - you will be able to access and run the ghauri with simple
ghauri --helpcommand.
Download Ghauri
You can download the latest version of Ghauri by cloning the GitHub repository.
git clone https://github.com/r0oth3x49/ghauri.git
Features
- Supports following types of injection payloads:
- Boolean based.
- Error Based
- Time Based
- Stacked Queries
- Support SQL injection for following DBMS.
- MySQL
- Microsoft SQL Server
- Postgre
- Oracle
- Supports following injection types.
- GET/POST Based injections
- Headers Based injections
- Cookies Based injections
- Mulitipart Form data injections
- JSON based injections
- support proxy option
--proxy. - supports parsing request from txt file: switch for that
-r file.txt - supports limiting data extraction for dbs/tables/columns/dump: swicth
--start 1 --stop 2 - added support for resuming of all phases.
- added support for skip urlencoding switch:
--skip-urlencode - added support to verify extracted characters in case of boolean/time based injections.
Advanced Usage
Author: Nasir khan (r0ot h3x49)
usage: ghauri -u URL [OPTIONS]
A cross-platform python based advanced sql injections detection & exploitation tool.
General:
-h, --help Shows the help.
--version Shows the version.
-v VERBOSE Verbosity level: 1-5 (default 1).
--batch Never ask for user input, use the default behavior
--flush-session Flush session files for current target
Target:
At least one of these options has to be provided to define the
target(s)
-u URL, --url URL Target URL (e.g. 'http://www.site.com/vuln.php?id=1).
-r REQUESTFILE Load HTTP request from a file
Request:
These options can be used to specify how to connect to the target URL
-A , --user-agent HTTP User-Agent header value -H , --header Extra header (e.g. "X-Forwarded-For: 127.0.0.1")
--host HTTP Host header value
--data Data string to be sent through POST (e.g. "id=1")
--cookie HTTP Cookie header value (e.g. "PHPSESSID=a8d127e..")
--referer HTTP Referer header value
--headers Extra headers (e.g. "Accept-Language: fr\nETag: 123")
--proxy Use a proxy to connect to the target URL
--delay Delay in seconds between each HTTP request
--timeout Seconds to wait before timeout connection (default 30)
--retries Retries when the connection related error occurs (default 3)
--skip-urlencode Skip URL encoding of payload data
--force-ssl Force usage of SSL/HTTPS
Injection:
These options can be used to specify which paramete rs to test for,
provide custom injection payloads and optional tampering scripts
-p TESTPARAMETER Testable parameter(s)
--dbms DBMS Force back-end DBMS to provided value
--prefix Injection payload prefix string
--suffix Injection payload suffix string
Detection:
These options can be used to customize the detection phase
--level LEVEL Level of tests to perform (1-3, default 1)
--code CODE HTTP code to match when query is evaluated to True
--string String to match when query is evaluated to True
--not-string String to match when query is evaluated to False
--text-only Compare pages based only on the textual content
Techniques:
These options can be used to tweak testing of specific SQL injection
techniques
--technique TECH SQL injection techniques to use (default "BEST")
--time-sec TIMESEC Seconds to delay the DBMS response (default 5)
Enumeration:
These options can be used to enumerate the back-end database
managment system information, structure and data contained in the
tables.
-b, --banner Retrieve DBMS banner
--current-user Retrieve DBMS current user
--current-db Retrieve DBMS current database
--hostname Retrieve DBMS server hostname
--dbs Enumerate DBMS databases
--tables Enumerate DBMS database tables
--columns Enumerate DBMS database table columns
--dump Dump DBMS database table entries
-D DB DBMS database to enumerate
-T TBL DBMS database tables(s) to enumerate
-C COLS DBMS database table column(s) to enumerate
--start Retrive entries from offset for dbs/tables/columns/dump
--stop Retrive entries till offset for dbs/tables/columns/dump
Example:
ghauri http://www.site.com/vuln.php?id=1 --dbs
Legal disclaimer
Usage of Ghauri for attacking targets without prior mutual consent is illegal.
It is the end user's responsibility to obey all applicable local,state and federal laws.
Developer assume no liability and is not responsible for any misuse or damage caused by this program.
TODO
- Add support for inline queries.
- Add support for Union based queries
Ghauri - An Advanced Cross-Platform Tool That Automates The Process Of Detecting And Exploiting SQL Injection Security Flaws
 Reviewed by Zion3R
on
8:30 AM
Rating:
Reviewed by Zion3R
on
8:30 AM
Rating:
 Reviewed by Zion3R
on
8:30 AM
Rating:
Reviewed by Zion3R
on
8:30 AM
Rating: